
Top 20 Cyber Security Interview Questions For Your Preparation
Introduction of Cyber Security Interview Questions It’s often said, ‘It takes 20 years to build a reputation and a few minutes of a cyber incident

Introduction of Cyber Security Interview Questions It’s often said, ‘It takes 20 years to build a reputation and a few minutes of a cyber incident

Introduction Walking into the world of cybersecurity needs more than just technical know-how; it demands a strong understanding of foundational concepts and problem solving skills.

Introduction In today’s digital world, where cyber threats are ever-changing and becoming more sophisticated, advanced security training is essential for threat awareness. Individuals who receive

Introduction SOC Analyst Job For Beginners Security Operations Center (SOC) is a professional who is the prime manager of the cyber security of a company

Introduction of Cyber Security Certification Training In the dynamic realm of cyber security, staying ahead of the curve is paramount. Cyber security certifications serve as

Introduction Mastering the SOC Analyst certification (Security Operations Center) path requires dedication, knowledge, and a deep understanding of cybersecurity concepts. By tracking, identifying, and handling

Introduction Cyber security has emerged as an immense issue for organisations attempting to protect their data and systems from ever-evolving threats in the current interlinked

Introduction In the era dominated by digital innovation, the demand for cybersecurity professionals has skyrocketed. As businesses grapple with the ever-present threat of cyberattacks, the

Introduction Cybersecurity has become important in today’s digital world. Individuals and companies must prioritize the security of their digital assets as cyber threats become more

We are in the internet generation and are fond of having our data at our fingertips. Since virtualization has simplified our lives, we are also
Expert Guidenace?

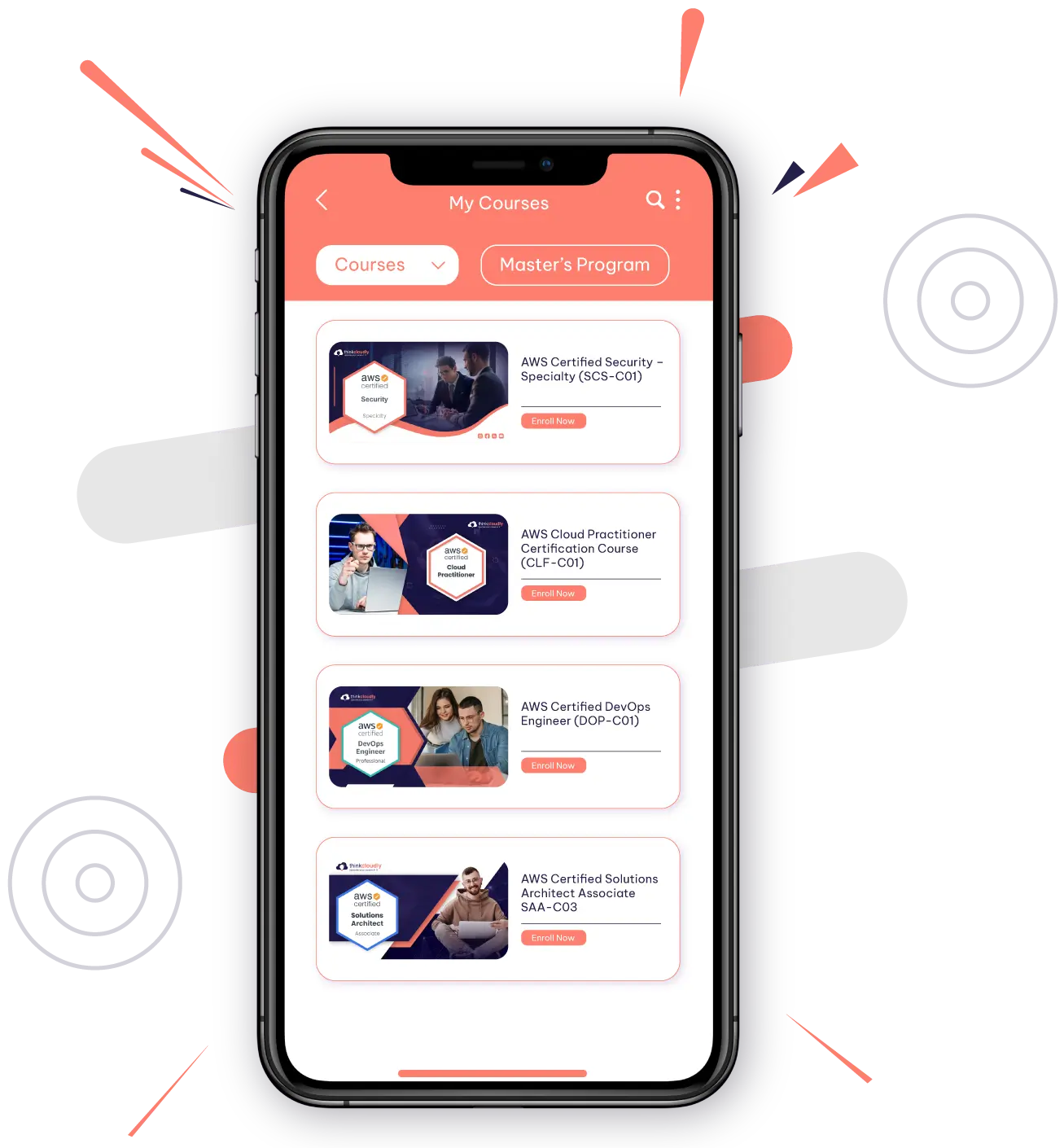
Download Thinkcloudly App today for enhanced experience on the go!




