Knowledge Center
Knowledge Center
How to Freelance as a Cloud Engineer in 2026 — Rates, Platforms, and First Client
The cloud industry is not waiting for anyone. Every week, another batch of companies shifts their operations online — and they all need skilled people

Serverless, Edge, and AI — The Three Forces Reshaping Cloud Careers Right Now
Cloud computing used to have a clear job description. You managed servers, kept systems running, and made sure data was stored safely. That was enough.
Top 10 AI Text Generation Tools in 2026 Everyone Is Talking About
Everyone is writing more in 2026. Blog posts, newsletters, social media content, product descriptions, sales emails, documentation — the demand for written content has never

AWS DevOps Certification (DOP-C02): Complete 2026 Guide
Three years ago, the average AWS DevOps engineer in the US earned around $117,000. Today that number is $131,698 — and certified professionals at the
10 Best AI Video Generation Tools in 2026
Video used to require a camera, a crew, editing software, and weeks of production time. In 2026, you type a sentence and get a clip

Top 10 Best AI Image Generation Tools in 2026 (Free & Paid)
In 2026, AI image generation has moved from an experiment to a daily creative tool. Marketing teams use it for campaign assets, designers use it

The $170K IT job most people have never heard of
Imagine starting your workday by fixing a bug in a code sample, then spending your lunch break filming a quick explainer video for YouTube. By
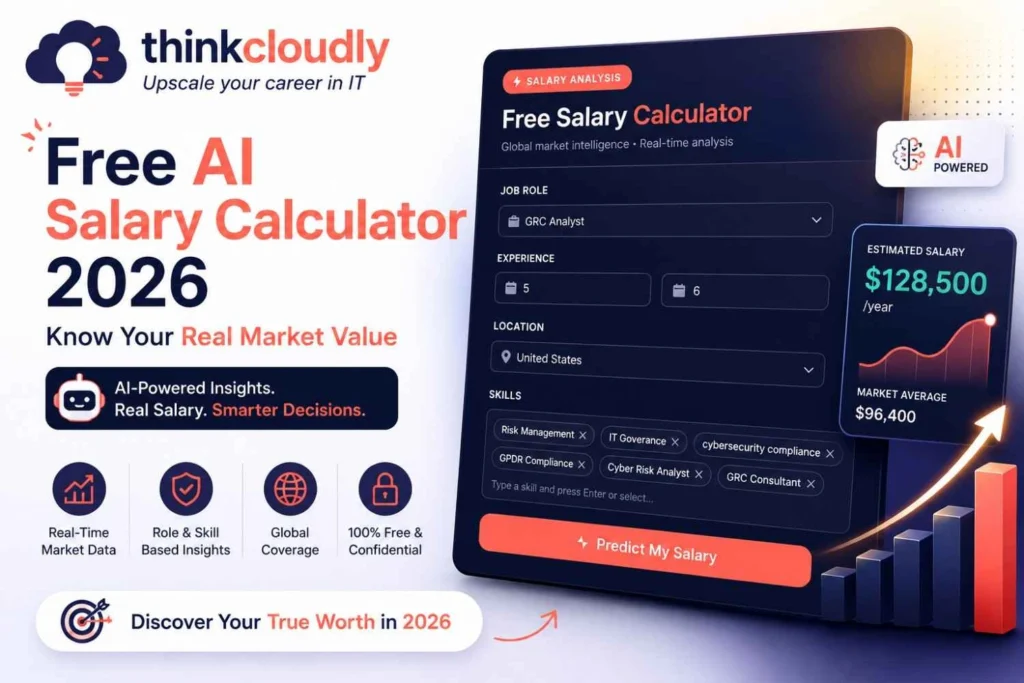
Free AI Salary Calculator 2026 — Know Your Real Market Value
Stop guessing. Start knowing. The job market has changed dramatically—and your paycheck should reflect that. If you’ve ever walked out of a salary negotiation
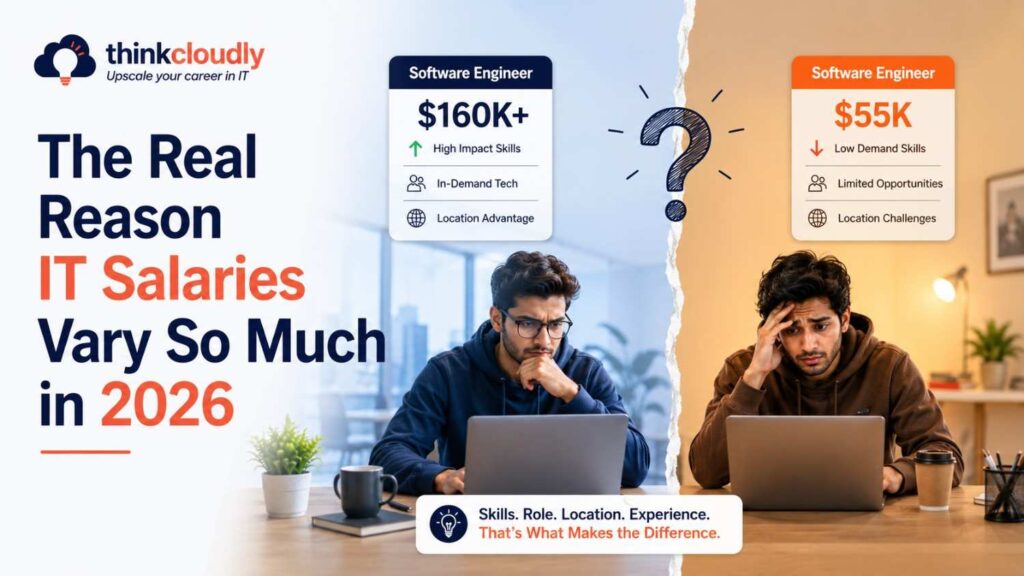
Why the Same IT Job Title Pays $60K at One Company and $120K at Another
Same job title. Same city. Same years of experience. But they are taking home twice what you are. It feels unfair—and sometimes it is. Most

Which IT Skills Are Growing Even During the Layoff Wave in 2026
Tech companies are laying off thousands and hiring frantically at the same time—here is what that actually means for your career. Open any news site
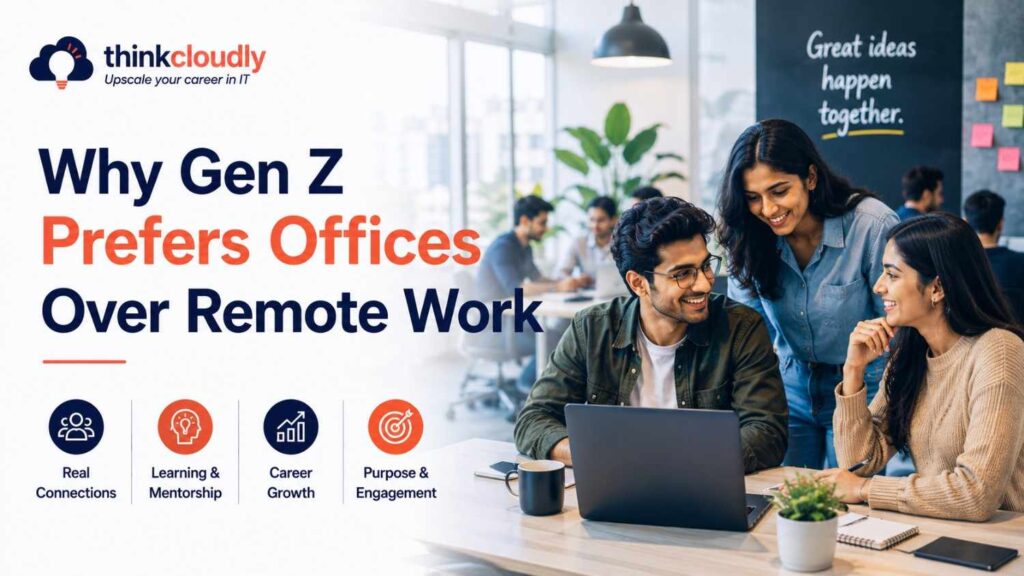
Why Gen Z Is Going Back to the Office While Senior IT Pros Stay Home
The generation that grew up online is choosing desks and commutes. The generation that fought for remote work is keeping it. Here is what is

Is a Tech Career Still Stable in 2026? Here’s What the Data Says
The layoff headlines make it easy to assume tech careers are falling apart. The data tells a more complicated, and far more useful, story. If

Getting Laid Off From Tech in 2026 Hits Different — Here’s Why
There is a particular kind of disorientation that comes with being laid off from a technology company in 2026 that did not exist in

Why Tech Companies Are Blaming AI for Layoffs in 2026
Something big is happening in the tech world right now — and most people are getting only half the story. In just the first few

Companies Are Cutting Jobs to Fund AI — Here’s Who Gets Hired Instead
You’ve probably seen the news. Amazon let go of thousands of people. Meta cut jobs while spending more on AI than ever. Atlassian shrank its

92,000 Tech Jobs Were Cut in 2026 — So Why Are 275,000 Roles Still Open?
The headlines have been alarming. Google cut thousands of positions. Microsoft reduced headcount across multiple divisions. Meta trimmed roles it had filled just two years

Top 10 AI Tools for Database Management in 2026
Data has become the most critical asset most organizations manage. But raw data is only useful if you can trust it, query it quickly, keep

39% of Your IT Skills Will Be Outdated by 2030
Imagine spending years building up a skillset — learning the tools, the frameworks, the workflows — and then one day realizing the industry has quietly

Top 10 AI Tools for Software Testing in 2026 (Automate & Accelerate)
Software teams in 2026 ship faster than ever. Daily releases, continuous deployment, and shrinking sprint cycles mean that manual testing can no longer keep up.

Google Cloud Is Growing Faster Than AWS in 2026 Job Market
A decade ago, someone told you to get AWS certified. They were right. In 2026, that advice needs an update. Google Cloud job postings grew

Why Getting More IT Experience Is No Longer Enough in 2026
Five years of solid IT experience. Strong certifications. A clean track record. And somehow—you didn’t make the shortlist. In 2026, this is not bad luck.

The IT Jobs Being Quietly Deleted in 2026 – And What’s Replacing Them
Nobody is making announcements. There are no dramatic press conferences, no industry-wide warnings, no headlines telling you that something fundamental has changed. And yet, if

IT Grew From 1 Million AI Jobs to 7 Million in 2 Years
Two years ago, listing “AI” on your resume made you stand out. Hiring managers leaned forward. Recruiters took notice. It was a signal that you

7 IT Jobs That Will Grow 300%+ by 2030
Hospitals are using AI to flag patient risks. Banks are using it to approve loans in seconds. Law firms are using it to scan thousands
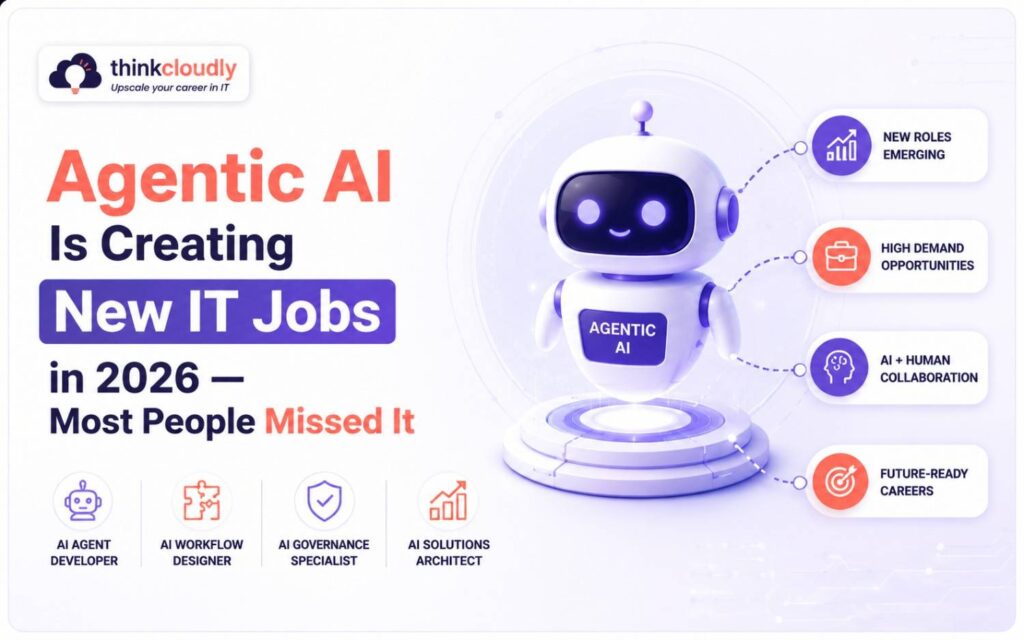
Agentic AI Is Creating New IT Jobs in 2026 — Most People Missed It
That’s the headline everyone keeps seeing. And honestly, it’s not completely wrong—AI is changing some roles. But here’s what’s flying under the radar: agentic AI

61% of Tech Companies Are Hiring Right Now — Why Aren’t You Getting Calls?
You’ve sent out 50 applications. You’ve refreshed your inbox every hour. You’ve updated your resume three times. Still silence. Meanwhile, your LinkedIn feed is full
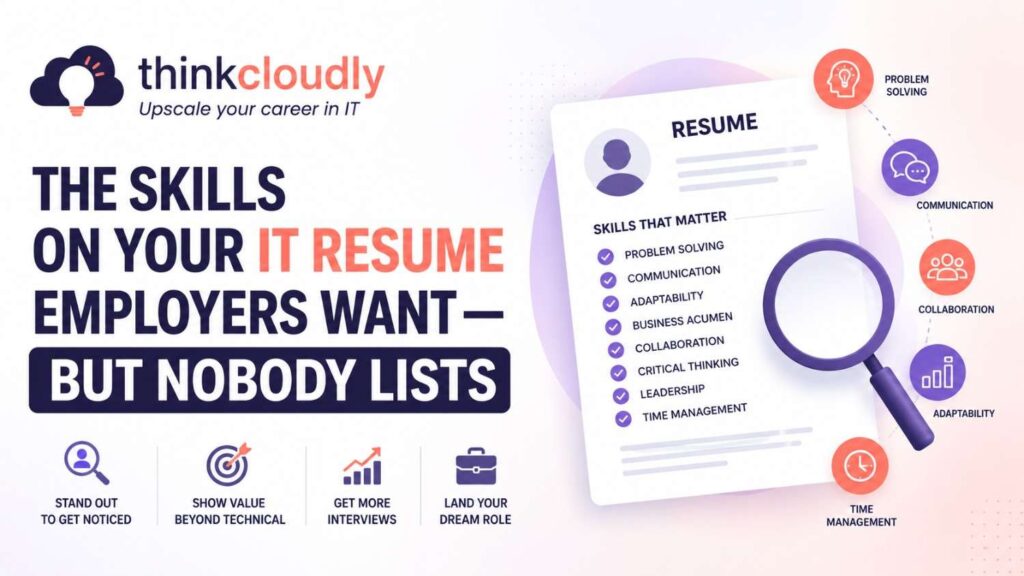
The Skills on Your IT Resume Employers Want — But Nobody Lists
You apply for an IT job. You have the right certifications. You know the tools. But you hear nothing back. Meanwhile, someone with fewer certifications

AWS Solution Architect Certification 2026: The Complete SAA-C03 Exam Guide
The AWS Solution Architect Certification is the most sought-after cloud credential in the world right now—and 2026 is the best year to earn it. According

Top 10 AI Cybersecurity Tools in 2026: Stay Safe, Stay Ahead
Cyberattacks in 2026 are faster, smarter, and more damaging than anything seen before. Attackers now use artificial intelligence to create novel malware, craft convincing phishing

The Soft Skill That’s Now Getting IT Professionals Hired Faster
Imagine two IT professionals applying for the same job. Both had the same certifications. Both passed the same technical tests. One gets hired in a

10 Best AI Tools for Project Management in 2026
Managing projects in 2026 looks completely different from just two years ago. Missed deadlines, unclear task ownership, overloaded team members, and endless status update meetings
Is an IT Career Still Worth It Starting in 2026?
Maybe you’ve heard the same two stories in the last few months. Story 1: “AI is killing IT jobs. Don’t even bother starting now.” You

Why Platform Engineering Pays More Than DevOps in 2026
You did everything right. You learned Docker, mastered CI/CD pipelines, and stayed late to fix broken deployments. You called yourself a DevOps engineer. And then,

IT Salaries Are Rising 8–10% in 2026 — But Not for Everyone
If you work in IT and haven’t seen a raise lately, 2026 may be the year that changes, but only if you’re in the right

Why Remote Cloud Jobs Are Still Hireable in 2026
Every week, someone lands a cloud engineering job from their spare bedroom — no commute, no office, and a salary that beats most of their
The 5 IT Skills Appearing Most in 2026 Job Postings (Based on Hiring Trends)
If you’re a student or fresher trying to figure out which IT skills to actually focus on, this blog will save you a lot of

10 Best AI Tools for IT Interview Preparation in 2026
There is a particular kind of silence that follows a question you thought you knew the answer to. The answer is somewhere — you studied

IT Skills That Grew 400% on Job Listings in One Year
Some IT skills are growing so fast in 2026 that companies cannot find enough people to hire. According to Dice’s April 2026 US Tech

DevSecOps Is the Role Replacing DevOps — Here’s What It Pays
If you have been working in tech for a few years, you have probably noticed something. The job postings that used to say “DevOps Engineer”

The Biggest Mistake IT Beginners Are Making in 2026
Sarah had been studying IT for seven months. She watched hours of tutorials every evening after her shift at a retail store. She took notes.