Hello AWS fan! You have recently created your first AWS S3 bucket and now you want to configure the S3 bucket policy to make it secure. How can I do it? What are policies? If you are struggling with the same questions then here is an article that will help you to get started with Bucket Policy in detail.
To enhance your guide on creating an S3 Bucket Policy, it’s essential to mention that AWS provides a powerful tool called the “AWS Policy Generator for S3,” which simplifies the process of crafting precise IAM policies for your S3 buckets. This user-friendly, web-based AWS S3 Policy Generator allows you to define fine-grained permissions, including read, write, and delete operations, and then generates the corresponding JSON policy document that you can apply to your S3 buckets. By leveraging this AWS S3 Policy Generator, you can streamline and optimize your S3 bucket policy creation process, ensuring secure and granular access controls for your objects stored in AWS S3.
“Streamlining S3 Bucket Policies with AWS Policy Generator”
“Crafting precise policies for your AWS S3 buckets is made easier with the AWS Policy Generator for S3. Whether it’s setting access controls, defining permissions, or managing data encryption, this tool simplifies the process. By inputting your desired configurations, the Policy Generator generates JSON policies that align with your requirements. These policies act as the guardrails for your S3 buckets, ensuring secure data management while adhering to compliance standards. With the AWS Policy Generator for S3, you can confidently tailor access and permissions to your specific needs, enhancing the security and integrity of your stored data.”
What Is Bucket Policy?
Before understanding what is Bucket Policy let’s understand the problem which we are trying to solve using Buckets policy, although it sounds strange but here goes…
An S3 bucket is something like a drive or folder where objects (files) will be stored. The problem comes when there should be some restriction on who or what should do uploads inside your bucket(especially if your files should not be visible to some specific people/users).
For example, if you have some confidential reports on your S3 bucket and at the same time, you want any of your AWS account holders to be able to download those files then without using Bucket Policies it will not be possible. You can go with the option of individual user access policy or use IAM policies but that’s it. There will be no restriction from uploading stuff inside your S3 bucket which you don’t want. This is where Bucket Policy comes into the picture and helps us achieve the desired result.
Bucket Policy: A collection of statements, evaluated one after another in order of appearance, that describes what a requester is allowed to do on a bucket and with each object contained in that bucket. It applies to a requester who has been authenticated to access the bucket in question.
In other words, Bucket policies are used to determine which user or service is allowed to access or perform actions on specific buckets and objects within that bucket. In this way, users can have fine-grained control over the retrieval of information from an AWS S3 Bucket
What Is Allowed By Default?
By default user is allowed to perform the following actions on all objects contained in a bucket:
- Delete object
- Create object
- List all the objects contained inside the bucket
- Get object metadata
- Put objects inside the bucket
- Delete all objects that he/she has uploaded inside the bucket.
Boost your earning potential with AWS expertise. Explore our certified AWS Courses for a high-paying career
So far so good. We have seen all that is allowed by default but where and how these permissions are configured?
You might be wondering, I am an AWS user and I created my S3 Bucket so where do these defaults come from/who configured them for me? All of this has been done by AWS itself while creating your bucket during its creation time. When you create a new bucket AWS verifies that it contains correct information and then configures some or all of the above-mentioned actions to allow YOUR-SELF(Owner) to perform all of them against that bucket. By default, the owner will be able to perform these actions on s3 objects however if required permissions can be expanded for specific use cases.
Who Can Configure These Permissions?
The bucket Policy attached to a bucket can be configured by the “Owner” of that bucket. This can be changed later if required. The owner can also update the policy but cannot delete it.
When you create the S3 Bucket AWS assigns a policy with some default permissions If an IAM user is associated with a bucket then he/she will have full permission on files inside the s3bucket irrespective of his/her role If no one is associated then the Owner will have all permissions.
What can you do with the Bucket Policy?
You can allow or deny specific actions against the s3 bucket and its objects. For example, if we want to create a policy that only allows uploading of files and nothing else (no delete, list, etc) then we can do that by specifying this in the policy.
How S3 Bucket Policies Work Under the Hood:
Policies work under the hood by configuring Access Control rules for buckets/objects inside that bucket. Each time a user tries to access an object AWS evaluates all built-in ACLs (if any) and then combined with configured policies permissions are granted. If no special permission is found then the default owner’s policy is applied.
Bucket policies are attached to the bucket while their access control rules are applied to objects inside the s3bucket. You do not need to specify a bucket policy for each object rather you can apply for default permissions at the bucket level and then override it with your custom policy when required.
Let’s start with the steps to add a bucket policy:
- Login to AWS Management Console and search S3.
- Create a bucket and give it a bucket name.
You can follow the steps given in Create S3 Bucket and Objects to create a bucket.
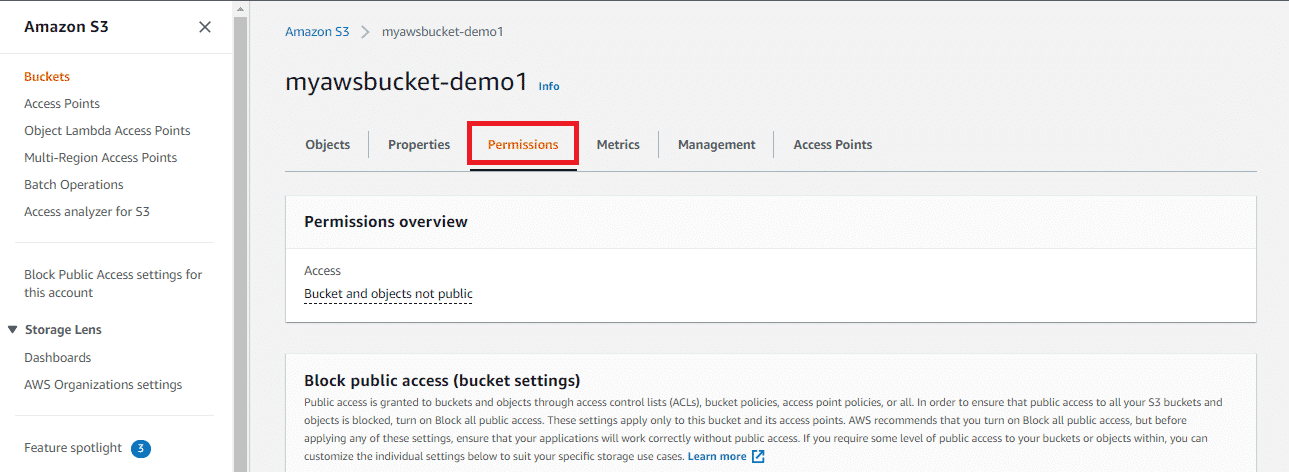
- In the S3 dashboard, click and access the bucket.
You will enter into your bucket dashboard and now you are ready to make changes and add bucket policies.
- Click on Permissions.
5. You can see Bucket Policy. Click on Edit.
Now, you have two options either you can write your bucket policy in the editor as a JSON file or you can simply generate a policy using Policy Generator. Here we will continue with generating a policy.
- Click on Policy Generator.
A new tab AWS Policy Generator will open.
- Now you are required to configure some settings for generating policies. Select Policy Type as S3 Bucket Policy.
- Choose to Allow or Deny in Effect according to how you want to permit users to upload encrypted files or not.
 9. In principle you need to add IAM ARN ( Amazon Resource Name) or type ‘ * ’ to select all users by default
9. In principle you need to add IAM ARN ( Amazon Resource Name) or type ‘ * ’ to select all users by default
10. Select Actions from the drop-down list you want to choose and apply to the bucket or you can select All Actions.
- In Amazon Resource Name (ARN), enter the Bucket name to which the policy needs to be applied. You can go back to the previous tab to copy the Bucket name. Add /* after the bucket name to select all the objects and subfolders.
- Now, you can Add the Conditions (optional). (Based on this condition it will be decided whether the access should be denied or not.)
 13. Click on Add Statement and finally on Generate Policy.
13. Click on Add Statement and finally on Generate Policy.
You have successfully generated Bucket Policy. A Policy JSON Document will pop up on the screen like this :
- You just need to copy the same to the Bucket Policy editor.
Click on Save Changes.
Congratulations! You have created your first Bucket Policy.
Conclusion:
In this blog post, we’ve taken a deep dive into the intricacies of the S3 Bucket Policy. You can create your policy using these steps and you should be able to keep up with best practices for security in the cloud. If you have any questions or would like any help from our team, don’t hesitate to reach out!
Interested in learning more about cloud computing? Check out our blogs! We offer AWS, and Azure training so you can get the knowledge and rock your career.